Deposits in Hinkal.
Withdrawals in Hinkal.
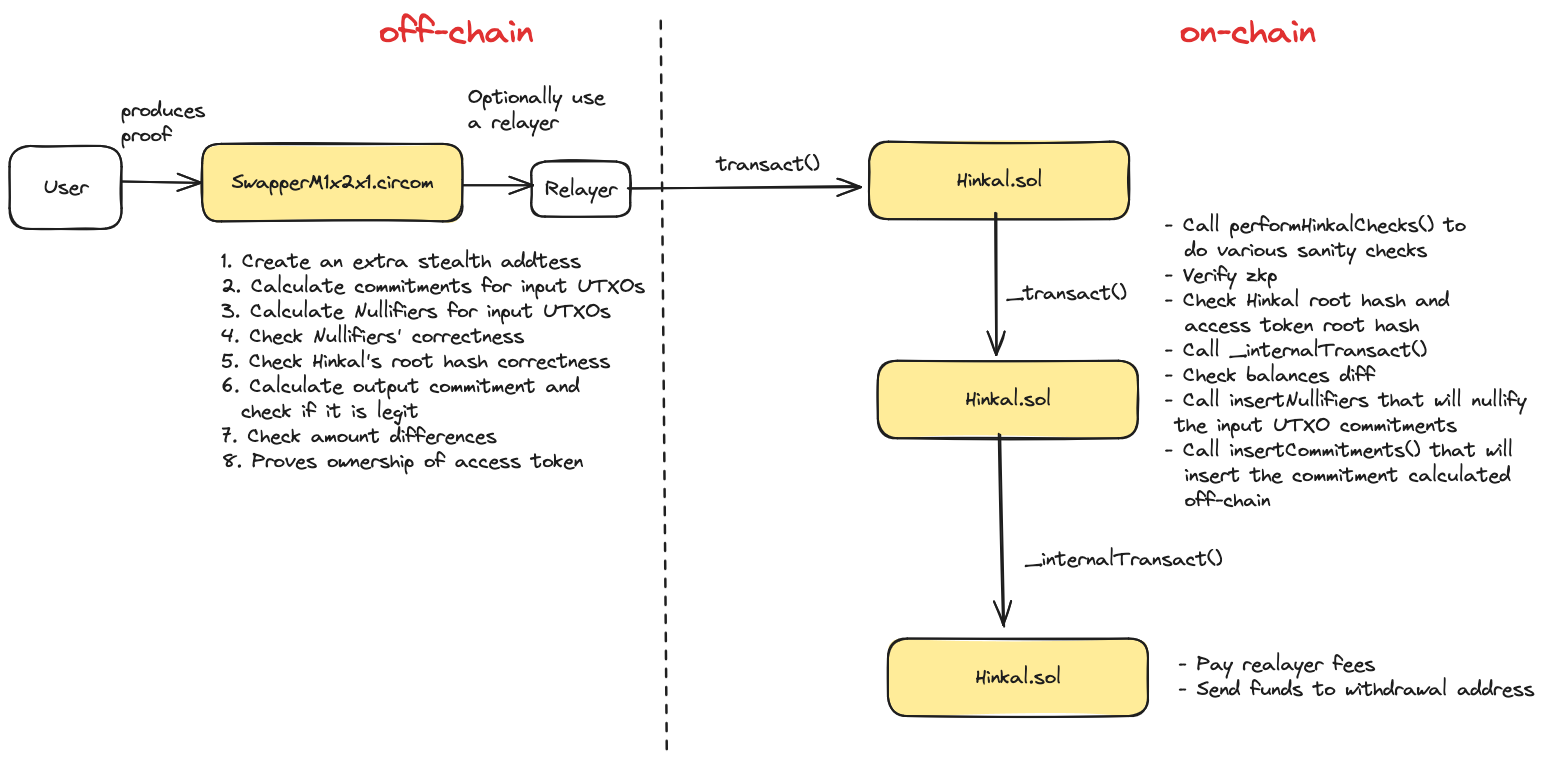
### Swapping in Hinkal The swapping process in Hinkal is similar to deposits and withdrawals, with a few key differences. Instead of using `SwapperM1x2x1.circom`, users will instantiate the `SwapperM` circuit with multiple tokens. Additionally, instead of calling the `_internalTransact()` function, the protocol calls `_internalRunExternalAction()`, which forwards the swap operation to `ExternalActionSwap:runAction()` (out of scope for this audit). This function executes the swap and returns the output UTXOs, which cannot be computed off-chain due to the variability of real-time token prices. Using these UTXOs, the output commitments are then generated on-chain and inserted into Hinkal’s Merkle tree. Unlike deposits and withdrawals, where output commitments are created off-chain during ZKP generation, swap-related commitments are computed directly on-chain after the swap is executed. ### Bridging in Hinkal Cross-chain bridging allows users to transfer funds between instances of the Hinkal contract across the chains where it is deployed. First, the user needs to produce two zero-knowledge proofs: - The first one proves that the user has some funds locked in the source chain in form of UTXOs, and provides nullifier checks for that UTXOs. This proof is produced using one of the `swapperM*` circuits, like any other external action. - The second one is a proof for ownership of the destination stealth address on the destination chain. This proof is produced using the `receiver` circuit. The relayer will initiate a normal external action on the source chain, and the main contract `Hinkal.sol` will verify ownership of funds, nullify UTXOs, and call the external action in the `ConnextAction.sol` contract (which implements the `IExternalAction` interface) using the `runAction()` function. The relevant data for the external action is stored in `externalActionMetadata`, which is then cast into an `ActionData` object. ```solidity struct ActionData { bool isReceive; bool unwrapNative; uint32 destination; uint slippage; uint rootHashHinkal; uint rootHashAccessToken; InternalProof internalProof; } ``` In particular this structure contains the `internalProof` which is the `receiver` zero-knowledge proof which will be sent cross-chain and will be verified on the destination chain. The `ConnextAction.sol` contract acts as the external action contract for both the bridge send and receive transactions. The two flows are distinguished by the `isReceive` flag in the action data structure. The `ConnextAction.sol` contract will, at this point, send a cross-chain invocation using a third-party bridging service called [connext](https://www.connext.network/). Invocation is done by calling the `connext.xcall()` function, which will invoke the `xReceive()` function on the `connextRescueBuffer.sol` contract deployed on the destination chain. According to the [connext documentation](https://docs.connext.network/developers/guides/handling-failures#reverts-on-receiver-contract) developers should use defensive strategies when implementing the `IXReceive` interface. Indeed, if a cross-chain receive transaction fails, then funds could get stuck on the receiver contract. The `connextRescueBuffer.sol` aims to address this issue by providing a safe buffer for funds. The Hinkal owner can re-try the failed transaction with a different `callData` (i.e., calling `rescue`) or directly withdraw them (i.e., calling `rescueAsset`). The rescue buffer keeps a mapping between the `transferId` provided by Connext and some information about the funds, in particular the amount, asset, and the original call data payload. The contract then calls the `transferCall()` function: if it succeeds then the mapping is removed, otherwise it is kept and a `FailedTransfer` event is emitted. At this point, the rescue buffer contract calls the `handleReceive()` function in the `ConnextAxtion.sol` contract (on the destination chain), also transferring the funds. This function basically prepares some input arguments and calls back into the normal `Hinkal.sol:transact()` transaction flow. The action ID is set to `RECEIVE_ONLY_ACTION_ID`, and the external action address is set to `this` (the `ConnextAction.sol` contract address). Crucially, the inner proof is also passed to the Hinkal contract as the main ZKP to be verified. The Hinkal contract performs verification of the zero-knowledge proof using the `receiver.circom` circuit, performs all the standard checks for the transact flow, and calls back the `ConnextAction.sol` contract as an external action. This call will generate the UTXO and will transfer back the funds from `ConnextAction.sol` contract to `Hinkal.sol` contract in the destination chain. The bridge of funds will be completed after Hinkal adds the out commitments in the new chain that are now spendable. Notice that if at any point the reception flow fails (e.g., because the inner proof is not valid), then the funds would still be locked in the rescue buffer. Below is a diagram of the bridging flow. 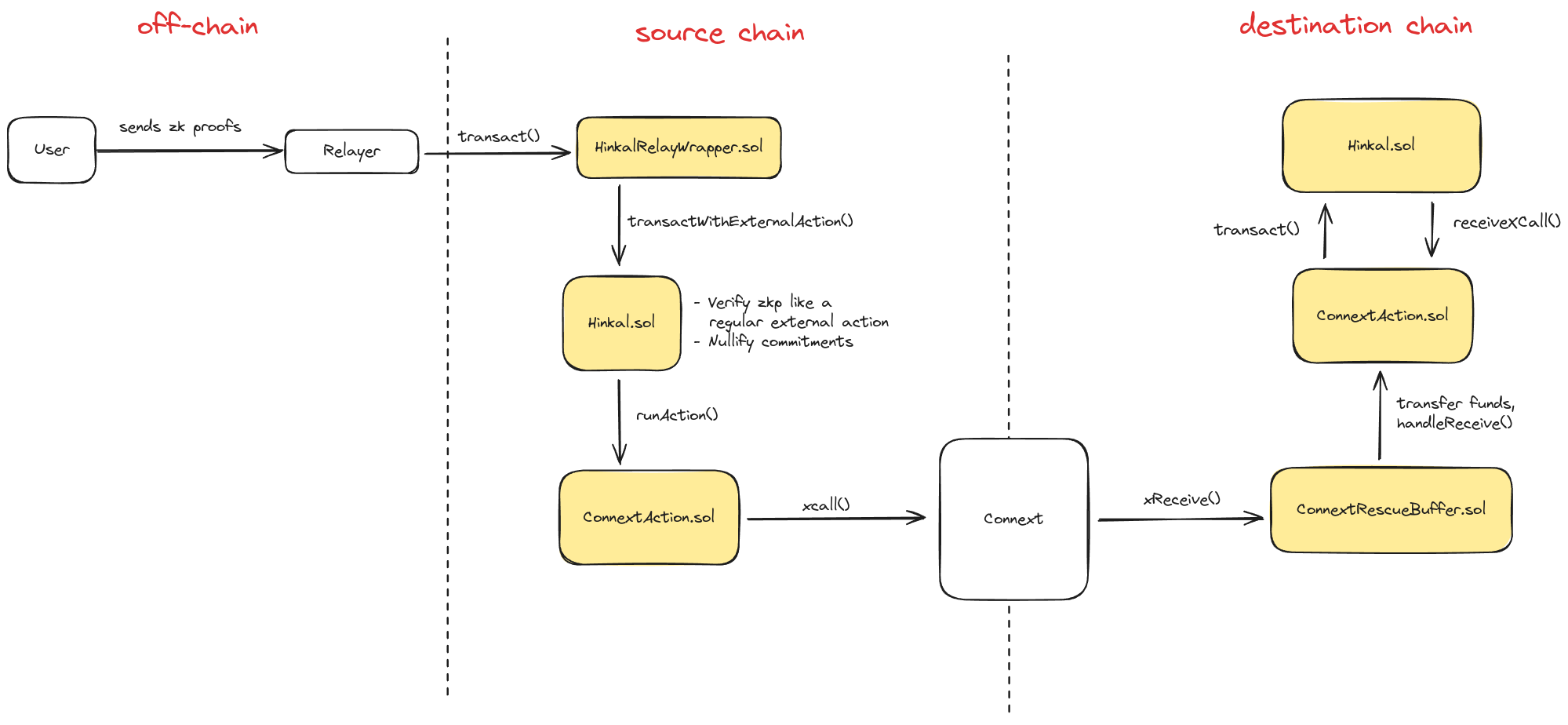 ### Staking in Hinkal Hinkal’s staking feature is designed to reward users who contribute to the protocol’s anonymity pool. Staking and deposit operations are managed through the `HinkalStakeExternalAction` contract, utilizing the `SwapperME1x2x1.circom` circuit. During a deposit, two commitments are generated: one for the standard Hinkal Merkle tree and another for the Hinkal staking Merkle tree. The first is a regular commitment, as previously described, while the second is an unspendable commitment placed in the staking Merkle tree, which cannot be minted. Similarly, when users stake their assets, they generate an unspendable deposit commitment in the Hinkal Merkle tree and a spendable commitment in the staking Merkle tree. These commitments are indistinguishable from external observers, enhancing the overall anonymity set of the Hinkal protocol. Upon staking, users can mint __hTokens__ (wrapped tokens) by spending their staking commitments. These hTokens can be used in DeFi protocols like any other token. Additionally, the Hinkal owner has the ability to distribute rewards to hToken holders. Finally, users can unstake their hTokens, converting them back into regular tokens and transferring them to any desired address. The figures below illustrate all the operations users can perform within the `HinkalStakeExternalAction` contract. 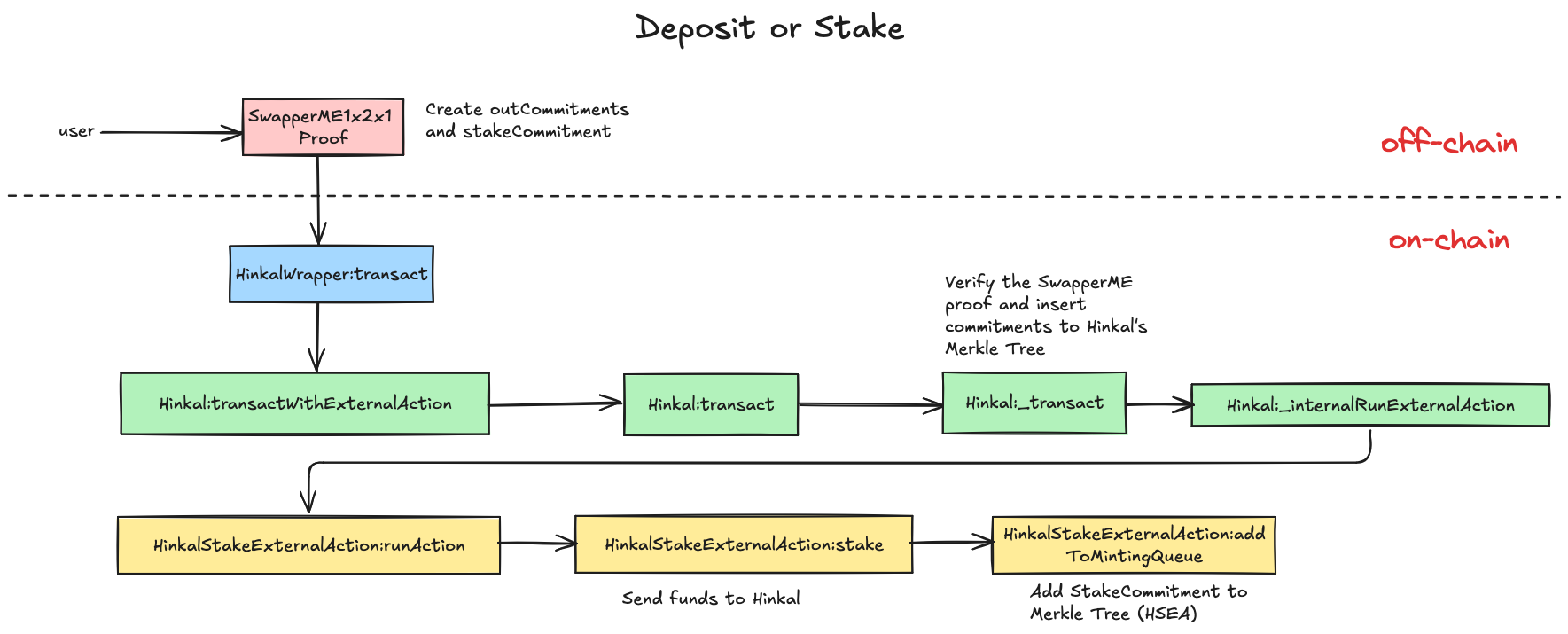 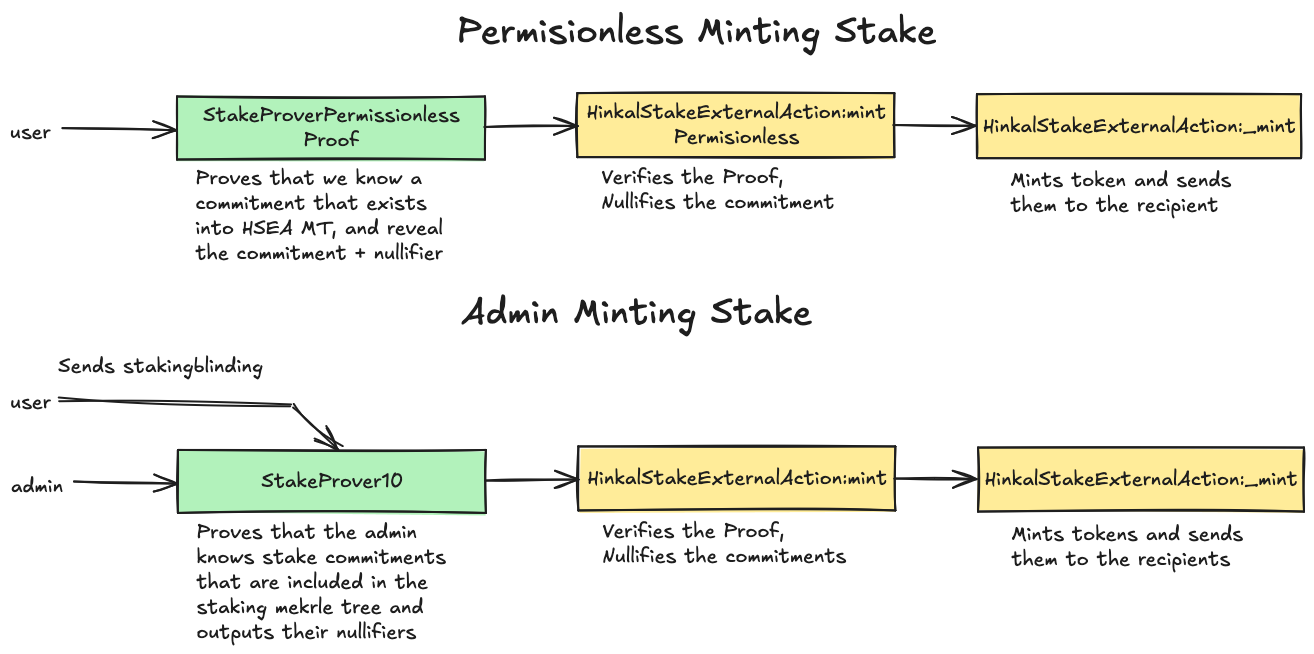 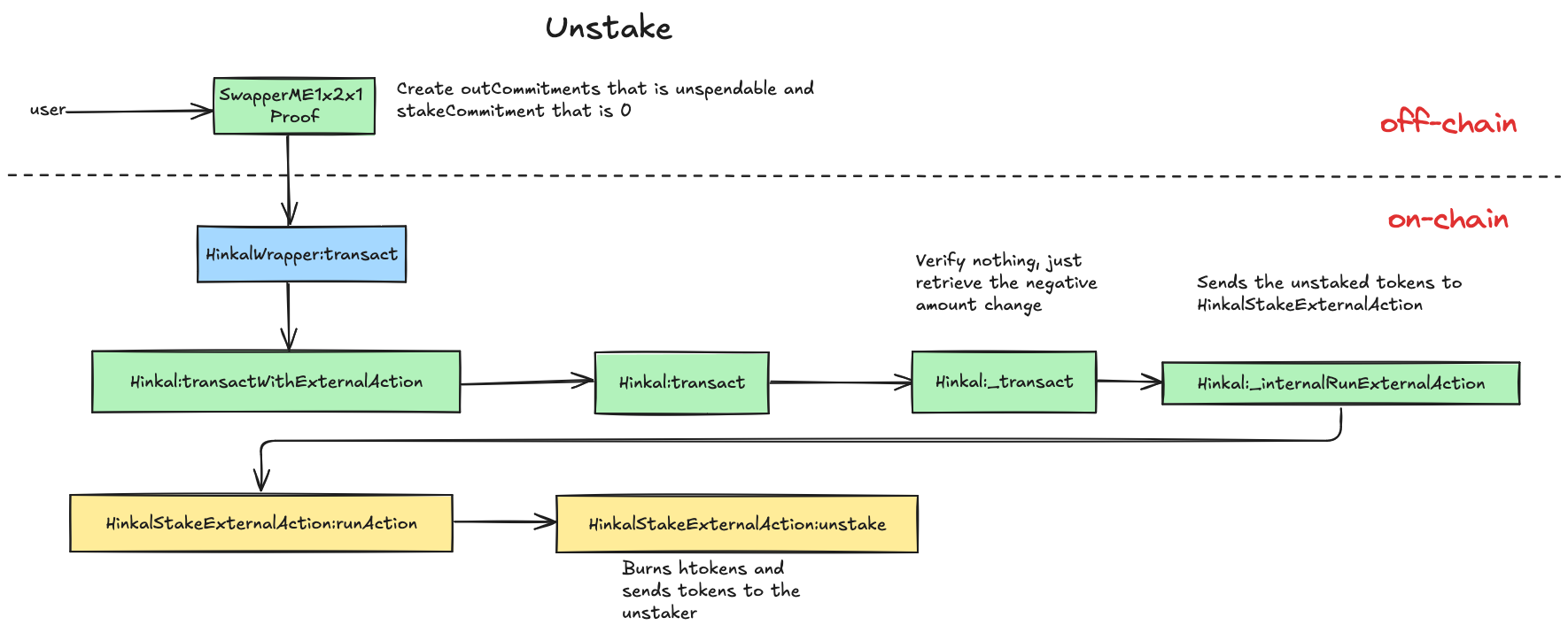 ## Findings ### The blacklisting mechanism is not enforced - **Severity**: Medium - **Location**: hardhat/contracts/CrossChainAccessToken.sol **Status**. Fixed. **Description**. The Hinkal protocol uses access tokens to authenticate participants who interact with Hinkal's contracts. The reason why Hinkal requires that authentication mechanism is that its users need to be KYC-ed in order to stay compliant with regulations. The way this process works is as follows: __off-chain steps:__ * The user interacts with a KYC provider to get KYC'ed. * The KYC provider creates a certificate for the user. * The user proves to the Hinkal server that he has been KYC'ed and sends his `AccessToken`, which is composed of his `shieldedPrivateKey` hashed with his `PublicKey` (which is the hash of his `shieldedPrivateKey`). * The server signs a message composed of the user's `AccessToken`, the `blockchain.chainid`, the Hinkal's protocol `CrossChainAccessToken` contract's `address`, and a `nonce`. __on-chain steps:__ * The user calls the `addToken` function of `CrossChainAccessToken` with the following data: ```solidity struct SignatureData { uint8 v; bytes32 r; bytes32 s; uint256 accessKey; uint256 nonce; } ``` * The `addToken` function does the following checks: ```solidity require(msg.value >= mintingFee, "minting fee not covered"); require( !blacklistAddresses[msg.sender], "Address has been blacklisted" ); require(!usedNonces[signatureData.nonce], "nonce already used"); bytes32 ethSignedMessageHash = getEthSignedMessageHash( signatureData.accessKey, block.chainid, address(this), signatureData.nonce ); address signer = recoverSigner(ethSignedMessageHash, signatureData); require( signer == owner(), "Signature must be signed by the owner of the contract" ); ``` * Then it calls the function `insertAccessToken` that will (i) insert the `AccessToken` in the Merkle Tree that stores the access tokens for compliant users, and will also add the `AccessToken`/`msg.sender` pair in the `accessTokens` mapping to map access tokens to addresses. The main issue in that process is that a malicious user can circumvent the blacklisting mechanism by just calling the `addToken` function by another address. **Impact**. This attack will lead to the Hinkal protocol being non-compliant by allowing non-blacklisted addresses to interact with the protocol. **Recommendation**. We recommend adding the `msg.sender` address in the signature to bind addresses to access tokens. By doing so, if the user uses another address to call the `addToken` function, then the signature verification will fail. * Client comment: We only use `blacklistAccessKey` as a blacklisting mechanism. `blacklistAddress` is a legacy function that we do not currently use. Given that we called `blacklistAccessKey` for a specific `accessKey`, the user who holds this access key will not be able to mint the access token again because he will not be able to use the same nonce. **Client Response**. Fixed in commit [cec95d4f443c6d5faed1d6d066c88bf92031f7d9](https://github.com/Hinkal-Protocol/Hinkal-Protocol/commit/cec95d4f443c6d5faed1d6d066c88bf92031f7d9). We added msg.sender in the signature to bind addresses to access tokens. ### encryptedOutput and encryptedStakeCommitmentContent are not binding to the verified ZKP proofs. - **Severity**: Medium - **Location**: hardhat/contracts/{Hinkal,external-actions/hinkal-staking/HinkalStakeExternalAction}.sol **Status**. Acknowledged. **Description**. All transactions in the Hinkal protocol are routed through `Hinkal.sol`. The process is the following: First, an off-chain ZKP proof is generated through the Circom circuits. The proof is then verified on-chain using the Solidity smart contracts, and some additional logic follows. When users transact with Hinkal, they are required to attach some additional data beyond the ZKP and the public inputs and outputs of the proof. Those data are the following: ```javascript externalActionMetadata -> calldata used with external actions stores information regarding swaps, route paths, and whether to perform staking / unstaking. externalActionId -> the id of the external action to use. externalActionAddress -> the address of the external action to use. flatFees -> the flat fees the client is willing to pay to the relayer relay -> the address of the relayer publicSignalCount -> used to determine which verifier to use. encryptedOutputs -> encrypted data used to store commitment information. ``` Then the hash of those data is also provided as a public input in the circuit as the signal `calldataHash`. Then the hash is also computed in the solidity code as follows. ```solidity function getHashedCalldata( CircomData calldata circomData ) internal pure returns (uint256) { return uint256( keccak256( abi.encode( circomData.publicSignalCount, circomData.relay, circomData.externalAddress, circomData.externalActionId, circomData.externalActionMetadata, circomData.hookData, circomData.encryptedOutputs, circomData.flatFees ) ) ) % CIRCOM_P; } ``` Those data are used mainly to prevent front-running issues and to bind the relay, hooks, and fees to the submitted proof computed off-chain by a user. Further, we understand that the `encryptedOutputs` are used for UI/UX purposes. For example, a user can query them to see which of those outputs have not been spent and are owned by a shielded address that they are owning. Nevertheless, those data are not bound to the circuit computations. That could lead to the attack scenario where an adversarial user that is participating in the Hinkal protocol computes off-chain a valid proof and then attaches to the proof the hash of the `circomData` where the `encryptedOutputs` are not the ones that supposedly should be. Note that the hash will be the same as the one used off-chain for producing the proof. Although all the checks will pass, the emitted `circomData.encryptedOutputs` won't be bound to the proof. __Note__ that an identical issue is happening with `encryptedStakeCommitmentContent` in `HinkalStakeExternalAction`. **Impact**. The attacker could achieve two goals. Firstly, it could trick another user into thinking that he has sent him some tokens because he can attach arbitrary UTXOs in the `encryptedOutputs`. Secondly, he can make the detriment any code that depends on the `encryptedOutputs` unusable by polluting `encryptedOutputs` of valid proofs with many incorrect UTXOs, which would result in users being unable to keep track of their real assets. Note that this issue could not exploit any of the functionality that is in the scope of this audit, i.e., it could not lead to double-spending, etc. Finally, note that users could actually check in the Merkle Tree if there are commitments for the UTXOs of `encryptedOutputs`. **Recommendation**. We recommend to bind `encryptedOutputs` in the Circom circuits. Otherwise, clearly document the above scenario, and implement tools for users to easily check the validity of `encryptedOutputs`. **Client Response**. We document the attack scenario in Risk Section, Point 6 (https://hinkal-team.gitbook.io/hinkal/hinkal/risks), and indicated a tooling for users to easily check the validity of `encryptedOutputs`. ### accessTokens mapping is not enforced to hold accurate data. - **Severity**: Low - **Location**: hardhat/contracts/CrossChainAccessToken.sol **Status**. Fixed. **Description**. In the code mentioned above (["The blacklisting mechanism is not enforced"](finding-blacklisting-issue)), for the same reason as above, the `accessTokens` mapping does not hold the supposed data. In our understanding, this map holds the data of which `accessToken` is owned by which address. A user can call the `addToken` function by another address, and then the access tokens mapping will not hold the correct data. **Impact**. This mapping is used in a required statement in `_migrateAccessToken` function: ```solidity require( accessTokens[accessKey] == msg.sender, "User does not own this access token" ); ``` Nevertheless, this should not lead to major issues as non-KYCed users cannot interact with the protocol as they do not have an access token. **Recommendation**. It is crucial to add the `msg.sender` address in the signature to bind addresses to access tokens. This will prevent a user from using another address to call the `addToken` function, as the signature verification will fail. **Client Response**. Fixed in commit [cec95d4f443c6d5faed1d6d066c88bf92031f7d9](https://github.com/Hinkal-Protocol/Hinkal-Protocol/commit/cec95d4f443c6d5faed1d6d066c88bf92031f7d9). We added msg.sender in the signature to bind addresses to access tokens. ### Merkle tree construction allows crafting a Merkle proof for membership of the intermediate nodes - **Severity**: Low - **Location**: libs/circom/MerkleRootCalculator.circom **Status**. Fixed. **Description**. The Circom template `MerkleRootCalculator` aims at reconstructing the Merkle tree root given a leaf and all the required intermediate hashes (i.e., siblings). The gadget computes this function (translated into pseudocode) ```python def MerkleRootCalculator(inCommitment, commitmentSiblings[inputs], commitmentSiblingSides[inputs]): hashes[0] = inCommitment for i in range(inputs): assert(commitmentSiblingSides[i] in [0, 1]) L, R = hashes[i], commitmentSiblings[i] if commitmentSiblingSides[i] == 1: R, L = L, R hashes[i+1] = Poseidon(L, R) if commitmentSiblings[i] == 0: hashesProcessed[i] = 0 else: hashesProcessed[i] = hashes[i+1] rootHashes[0] = hashes[0] for i in range(1, inputs+1): if hashesProcessed[i-1] == 0: rootHashes[i] = rootHashes[i-1] else: rootHashes[i] = hashesProcessed[i-1] return rootHashes[inputs] ``` The logic of the function allows to craft a Merkle proof for every intermediate node in the Merkle tree, thus proving membership of non-member values. The root cause is the fact that the root hash alone does not provide any information to the verifier about the current height of the tree. For example, take the Merkle tree formed by just two levels, where the leaves are, for simplicity, `1`, `2`, `3`, and `4`. ```javascript Tree leaves: - 1 - 2 - 3 - 4 Second level: - 7853200120776062878684798364095072458815029376092732009249414926327459813530 - 14763215145315200506921711489642608356394854266165572616578112107564877678998 Root - 3330844108758711782672220159612173083623710937399719017074673646455206473965 ``` We should be allowed to prove only membership of the leaves; for example, an intended usage would be proving membership of the value `1` by providing the following input. ```json { "inCommitment": "1", "commitmentSiblings": ["2", "14763215145315200506921711489642608356394854266165572616578112107564877678998"], "commitmentSiblingSides": ["0", "0"] } ``` We can, however, prove the membership of the root by providing a Merkle proof composed of only zeros. ```json { "inCommitment": "3330844108758711782672220159612173083623710937399719017074673646455206473965", "commitmentSiblings": ["0", "0"], "commitmentSiblingSides": ["0", "0"] } ``` Additionally, we can also prove membership of any intermediate node values by providing "half" of the Merkle proof and padding on the right with zeros. ```json { "inCommitment": "7853200120776062878684798364095072458815029376092732009249414926327459813530", "commitmentSiblings": ["14763215145315200506921711489642608356394854266165572616578112107564877678998", "0"], "commitmentSiblingSides": ["0", "0"] } ``` In all three cases, the `MerkleRootCalculator` circuit gives output the correct Merkle tree root hash value ```javascript rootHash = 3330844108758711782672220159612173083623710937399719017074673646455206473965 ``` The `AccessTokenChecker` circuit should check that the prover knows an opening to an access token commitment stored in a Merkle tree on-chain. The pseudocode of the checker is as follows. ```python def AccessTokenChecker(shieldedPrivateKey, publicKey, rootHashAccessToken, accessTokenSiblings[treeDepth], accessTokenSiblingSides[treeDepth], isStakeOrUnstake): # compute the token commitment from the opening calcAccessToken = Poseidon(shieldedPrivateKey, publicKey) # compute the Merkle root from commitment and the proof calcAccessRootHash = MerkleRootCalculator( inCommitment, commitmentSiblings[inputs], commitmentSiblingSides[inputs]) # check that the computed root is equal to the real one if isStakeOrUnstake == 0: assert(calcAccessRootHash == rootHashAccessToken) ``` As a consequence of the previous issue, it is possible to provide valid Merkle proof even without knowing the opening to a commitment in the Merkle tree. In this scenario, the attacker observes the AccesToken Merkle tree on-chain; suppose it's the one above where the token commitments are `1`, `2`, `3`, and `4`. Since the `MerkleRootCalculator` allows for proving membership of internal nodes of the tree, the tree itself provides valid openings for the access token. A valid input for the `AccessTokenChecker` template is as follows. ```json { "shieldedPrivateKey": "7853200120776062878684798364095072458815029376092732009249414926327459813530", "publicKey": "14763215145315200506921711489642608356394854266165572616578112107564877678998", "rootHashAccessToken": "3330844108758711782672220159612173083623710937399719017074673646455206473965", "accessTokenSiblings": ["0", "0"], "accessTokenSiblingSides": ["0", "0"], "isStakeOrUnstake": "0" } ``` Notice that every value is either fixed or derived from the (public) Merkle tree on-chain. Notice also that this is enabled by the token commitment being the result of hashing two field elements with the Poseidon hash, which is exactly equal to the Merkle tree hash computation at every node. Finally, this is vulnerable because there is no constraint in the circuit such that the public key is indeed derived from the private key. Hence, if there is such a check before calling this circuit (which is the case for Receiver and SwapperM), then this vulnerability is not exploitable. This is because in order to exploit it, we need to find intermediate hashes that the one is the Poseidon hash of the other. **Impact**. This issue allows the construction of valid Merkle proofs for intermediate nodes present in the tree. We did not find any instance of this being exploitable in practice: `AccessTokenChecker` is always used by having the `publicKey` generated from the `shieldedPrivateKey`. However, we recommend fixing this issue as the `AccessTokenChecker` could be reused in other contexts. If not fixed, we recommended adding a warning of the implicit constraint that `publicKey` must be derived from `shieldedPrivateKey`. **Recommendation**. Ensure that the Merkle root calculator computes correctly every hash at each level. This could be implemented by also providing to the Merkle root calculator an additional input specifying how many leaves are currently in the tree. The circuit should then check the length of the proof to be consistent with this value. **Client Response**. Fixed in commit [b22861f9e40725cdad96bee5d2b926abd928a90e](https://github.com/Hinkal-Protocol/Hinkal-Protocol/commit/b22861f9e40725cdad96bee5d2b926abd928a90e). We enforced the constraint that public key should be a derivation from private key in AccessTokenChecker circuit. ### Attacker can get ETH that was accidentally sent to HinkalWrapper - **Severity**: Informational - **Location**: hardhat/contracts/HinkalWrapper.sol **Status**. Fixed. **Description**. Suppose a user goes into unstake flow and he accidentally sends 1 ETH to `HinkalWrapper` as `msg.value`. This message value is stored in `HinkalWrapper` as a state variable named `value`. Since unstake flow does not use this ETH balance, it will stay one ether after the user transaction gets executed. Since `HinkalWrapper.getETH()` is permissionless, an attacker can call it and steal the user's ETH: ```solidity function getETH() public { uint256 oldValue = value; value = 0; transferETH(msg.sender, oldValue); } ``` **Impact**. If the user mistakenly sends some ETH to `HinkalWrapper`, an attacker can get them. **Recommendation**. Check who is `msg.sender` in the code: ```solidity // Add hinkalStakeExternalAction info via constructor function getETH() public { require(msg.sender == sender || msg.sender == address(hinkalStakeExternalAction), "unexpected caller"); uint256 oldValue = value; value = 0; transferETH(msg.sender, oldValue); } ``` **Client Response**. Fixed it in commit [a0ea50b328d101ca7e86910c274ca505ced5b1dc](https://github.com/Hinkal-Protocol/Hinkal-Protocol/commit/a0ea50b328d101ca7e86910c274ca505ced5b1dc). We added Roles to HinkalWrapper, so we restrict entities who can call getETH. ### SwapperME circuit is unnecessarily complex - **Severity**: Informational - **Location**: libs/circom/SwapperME.circom **Status**. Fixed. **Description**. The `SwapperME` circuit produces proofs for use with Hinkal staking features. Specifically, this circuit is responsible for creating and verifying proofs for depositing, staking, and unstaking in the staking extension of the Hinkal protocol. The circuit has some unnecessary complexity as its only instantiation is the following. ```javascript component main {public [rootHashHinkal, rootHashAccessToken, outTimeStamp, extraRandomization, amountChanges, erc20TokenAddresses, calldataHash, inNullifiers, outCommitments ]} = SwapperME(1,2,1,25); ``` Hence, the template variables `tokenCount`, `inputCount`, and `outputCount`, can be removed. Further, the `onChainCreation[tokenCount]` signal is enforced to always be `0` (i.e. `false`). This is enforced in `StakeInputChecker` template by using the following constraint. ```javascript isOnChainCreationZero[i] === 1; ``` We also recommend removing this signal and simplifying all the affected templates. Finally, the __unstake__ process does not require a ZKP to be verified. In the `SwapperME` circuit, all the important checks are being "disabled", and it essentially just produces a nullifier that does not nullify any __valid__ commitment. It also just checks the `amountChanges` correctness, but the user just provides this as a public input, so this check can also be applied in plain Solidity code. We recommend simplifying the circuit by removing the unstake functionality and handling unstake via Solidity. Note that if unstake is being removed, users will still have to go over the Hinkal contract to unstake, and they should __not__ have the ability to include nullifiers as this can lead to other issues in case of frontrunning. **Impact**. We did not find any vulnerabilities resulting from the complexity of the `SwapperME` circuit. **Recommendation**. We recommend refactoring the `SwapperME` circuit to reduce its complexity and reduce the possibility of introducing subtle issues in the future. **Client Response**. Fixed it in commit [e25c034f232849499308b6e2cd24ab63fc4cc9ec](https://github.com/Hinkal-Protocol/Hinkal-Protocol/commit/e25c034f232849499308b6e2cd24ab63fc4cc9ec). We simplified SwapperME by removing onChainCreation variable. We did not touch tokenCount, inputCount, and outputCount since we want to have possibility to extend circuits to multi-token staking. --- This report was published on the [zkSecurity Audit Reports](https://reports.zksecurity.xyz) site by [ZK Security](https://www.zksecurity.xyz), a leading security firm specialized in zero-knowledge proofs, MPC, FHE, and advanced cryptography. For the full list of audit reports, see [llms.txt](https://reports.zksecurity.xyz/llms.txt).